The Daily Reality of Modern IT Operations
An employee reports they can’t sign in.
The help desk sees repeated MFA failures. Authentication logs show rejected attempts. The immediate assumption: user error or credential issues. A ticket is opened.
Support resets credentials. The user tries again. Still failing.
Another team reviews the identity logs. Nothing obviously wrong appears.
Eventually someone notices that earlier in the morning a Conditional Access policy was updated, blocking unmanaged devices from accessing certain applications. That change inadvertently affected a large group of users whose device compliance status had not yet updated.
What appeared to be an authentication issue was actually a device compliance policy interaction triggered by an identity policy change.
But discovering that required:
- Identity logs
- Device management data
- Policy configuration history
- Endpoint compliance status
- Timeline correlation
Most organizations don’t investigate incidents that way. They simply treat the symptom and move on.
What Is IT Root Cause Analysis (RCA)?
IT root cause analysis (RCA) is the process of identifying the underlying cause of an incident or operational disruption rather than merely addressing its symptoms.
In modern enterprise environments, incidents often span multiple services (e.g., identity, applications, infrastructure, device management). Effective root cause analysis therefore requires correlating signals across systems to understand what triggered the failure, not just where the alert appeared.
When root cause analysis fails, teams may resolve the visible issue but leave the underlying problem intact leading to repeated incidents and increased operational risk.
Why Root Cause Analysis Breaks Down in Modern IT Environments
Traditional IT root cause analysis assumes something simple: the system generating the alert is the system causing the problem.
That assumption worked when infrastructure was simpler. But modern enterprise environments are fundamentally different. Today’s operational ecosystems include:
- Identity platforms (e.g., Entra ID)
- Productivity & collaboration tools (e.g., Microsoft 365)
- Endpoint telemetry from Windows devices
- Device management (e.g., Intune)
- Cloud infrastructure (e.g., Azure)
- Service management systems (e.g., ServiceNow)
Each platform produces its own telemetry, alerts, and logs. But incidents rarely respect those boundaries. A policy change in one system may cascade through several others before anyone notices the symptoms.
The result is a familiar pattern. Teams chase alerts inside individual systems, while the true root cause exists somewhere else entirely.
The Hidden Cost of Broken Root Cause Analysis
When root cause analysis fails, the damage extends beyond a single incident. The operational impact compounds quickly.
Mean Time to Resolution (MTTR) Increases
Investigations require jumping between dashboards, exporting logs, and manually correlating timestamps. Engineers spend hours reconstructing timelines.
Escalations Increase
Frontline support often cannot determine the root cause because the investigation requires data across multiple systems. Tickets escalate to senior engineers, consuming valuable expertise.
Incidents Recur
If the real cause is never identified, the same issue resurfaces repeatedly. Support teams may “fix” the visible problem without eliminating its origin.
Teams Lose Confidence in Alerts
When alerts frequently misrepresent the true issue, teams begin to distrust their monitoring tools.
Eventually the alert stream becomes noise rather than insight.
Lacking Correlation Insight Across Systems
Most organizations already have extensive monitoring tools. They can see identity events. They can see application errors. They can see device compliance status. But those signals exist in isolation. What’s missing is the ability to reason across them.
The real challenge in modern root cause analysis isn’t collecting data. It’s understanding how events across multiple services connect over time.
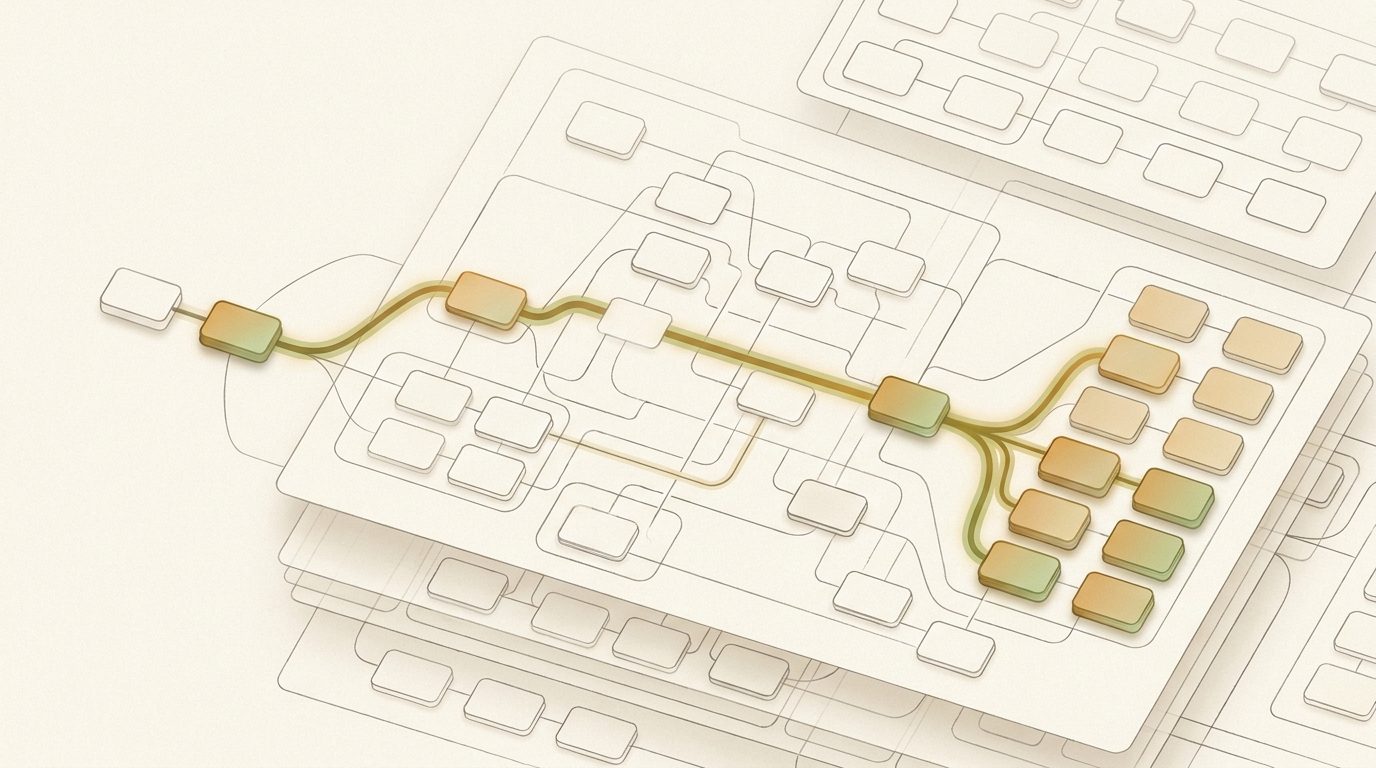
Consider how a typical incident unfolds:
1. A configuration change is made in one system.
2. A downstream service behaves differently.
3. End users experience failures.
4. Alerts appear in an entirely different platform.
Without correlation, each signal appears unrelated. With correlation, a clear narrative emerges.
The Ideal State: Cross-System Root Cause Intelligence
Imagine investigating incidents differently.
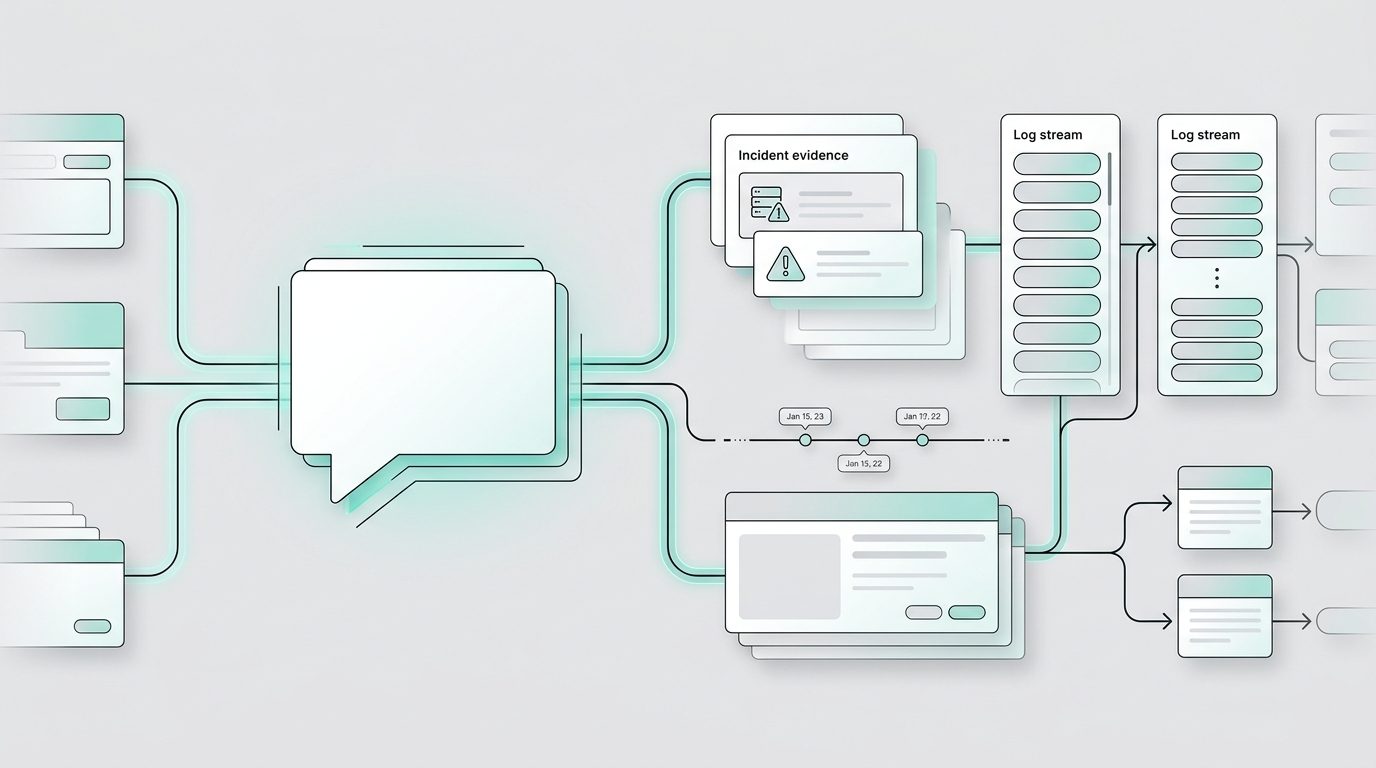
Instead of jumping between consoles, exporting logs, and manually reconstructing timelines, the system itself understands the relationships between services. An investigation might begin with a simple question: Why are MFA failures suddenly increasing?
Instead of returning raw logs, the system analyzes activity across multiple services. It detects a policy change applied earlier in the day. It recognizes that the change affected unmanaged devices. It correlates that condition with authentication failures appearing minutes later. And it presents a clear explanation:
“MFA failure spike correlates with Conditional Access update applied to unmanaged devices at 9:42 AM.”
The investigation shifts from data gathering to decision making. This is the core promise of operational intelligence.
Introducing Panorama AI: A New Approach to Root Cause Analysis
To address these challenges, a new approach to IT root cause analysis is emerging. Instead of analyzing signals within individual platforms, operational intelligence systems reason across service boundaries.
Panorama AI was built with that principle in mind. Rather than functioning as another monitoring tool, it acts as an investigative layer across enterprise systems. It analyzes signals from platforms including:
- Entra ID
- Microsoft 365
- Windows endpoints
- Intune
- Azure
- ServiceNow or Dynamics Customer Service
Its goal isn’t simply to display alerts. It reconstructs event chains that explain how incidents occurred.
How Panorama AI Enables Modern IT Root Cause Analysis
Panorama AI approaches root cause analysis differently. Instead of treating alerts as isolated signals, it analyzes the relationships between events across identity, application, device, and policy layers. Several capabilities make this possible:
Cross-Service Correlation
The platform correlates events from multiple services to determine how changes in one system affect another.
A policy update, endpoint state change, or application deployment can all influence downstream behavior. Panorama AI evaluates those relationships automatically.
Timeline Reconstruction
Incidents rarely occur instantaneously. They unfold through a sequence of events.
Panorama AI builds chronological event chains that connect:
- Configuration changes
- System events
- User activity
- Service alerts
This timeline helps investigators quickly understand how an issue evolved.
Impact and Blast Radius Analysis
When an operational change introduces a problem, the immediate question becomes: Who or what is affected?
Panorama AI evaluates the blast radius by identifying impacted:
- Applications
- Users
- Devices
- Policies
Teams can determine the scope of an incident within minutes.
Evidence-Based Root Cause Identification
Instead of presenting generic alerts, the system evaluates evidence across services to determine the most likely root cause. Investigators receive structured explanations rather than fragmented logs.
This reduces ambiguity and speeds resolution.
A Workflow Example: From Alert to Explanation
Consider a real-world workflow.
Step 1: An Incident Appears
Helpdesk notices a spike in sign-in failures. Authentication alerts appear in the identity platform.
Step 2: Panorama AI Correlates Signals
The system analyzes recent activity across connected services. It detects:
- A Conditional Access policy update
- Changes to device compliance rules
- A surge in authentication failures shortly afterward
Step 3: Event Chain Is Built
Panorama AI connects these events into a timeline:
1. Device compliance policy modified
2. Conditional Access rule updated
3. Unmanaged devices fail compliance check
4. MFA failures increase
Step 4: Root Cause Is Identified
The platform presents a structured explanation linking the policy change to authentication failures.
Investigators no longer search for clues. They evaluate a coherent narrative.
The Operational Impact
Improving root cause analysis produces measurable operational benefits for IT. Organizations using cross-system operational intelligence often see improvements across several areas:
Faster Incident Resolution
Automated correlation reduces the time required to reconstruct incident timelines. This directly lowers Mean Time to Resolution (MTTR).
Reduced Escalation Rates
Frontline support teams can resolve more incidents independently when the system provides structured explanations.
Better Use of Engineering Time
Senior engineers spend less time performing manual log analysis and more time addressing strategic improvements.
More Accurate Root Cause Diagnoses
Root causes are identified based on evidence across multiple systems rather than assumptions derived from single alerts.
Fewer Recurring Incidents
When the underlying root cause is addressed, repeat issues become less common. Teams spend less time revisiting the same problems.
Example Outcomes from Early Deployments
Organizations leveraging cross-system operational intelligence have reported significant operational improvements.
In several environments:
- Incident investigation time dropped by more than 60%
- Helpdesk escalations related to configuration changes decreased
- Repeat incidents declined significantly
Support teams also reported a notable shift in workflow. Instead of spending time locating data, they focused on interpreting it.
This distinction is subtle but important. It transforms incident response from forensic reconstruction into informed decision-making.
Why This Shift Matters Now
Enterprise environments are only becoming more interconnected. Identity platforms influence application access. Device management policies affect authentication. Cloud configuration changes ripple through SaaS services.
As complexity grows, traditional approaches to IT root cause analysis struggle to keep up. Organizations need systems that understand relationships between services rather than analyzing them individually.
Operational intelligence provides that connective layer. It enables teams to see the whole system, not just the tools they use to manage it.
Quick Recap: What Cross-System Root Cause Intelligence Delivers
Operational intelligence platforms such as Panorama AI help modernize root cause analysis by enabling teams to:
- Correlate events across identity, application, device, and policy layers
- Reconstruct incident timelines automatically
- Identify likely root causes with supporting evidence
- Evaluate blast radius across users and devices
- Reduce investigation time and incident recurrence
Instead of isolated alerts, teams receive clear explanations of what happened and why.
Spend Less Time Trying to Understand the Cause and More Time Solving the Problem
The future of IT root cause analysis lies in understanding systems as interconnected environments rather than isolated platforms.
Operational intelligence enables organizations to move beyond reactive troubleshooting and toward deeper operational insight. When incidents occur, the question shifts from “What changed?” to “How do we best solve the problem?” That difference is what transforms incident response from guesswork into clarity.
Operate Your Microsoft Environment with Clarity
Panorama AI is an operational intelligence layer purpose-built for IT teams managing complex Microsoft ecosystems and spending too much time addressing change-related incidents.
Panorama AI eliminates the visibility gap across Microsoft services and endpoints to provide a unified system view, including granular configuration intelligence, complete change transparency, and persistent operational memory of every incident and resolution.
By combining natural language investigation with advanced AI, Panorama AI empowers IT teams to reduce investigation times, escalations, and MTTR (Mean Time to Resolution). Through tenant-specific cross-service root cause intelligence and proactive configuration drift monitoring, Panorama AI reduces incident frequency (both new and repeat incidents).
No more chasing alerts. No more jumping between tools. No more manually reconstructing timelines.
Instant understanding of what changed, what it impacted, and how to fix it.
Schedule a demo or connect with one of our experts today to see how you can bring clarity, speed, and control to your operations.