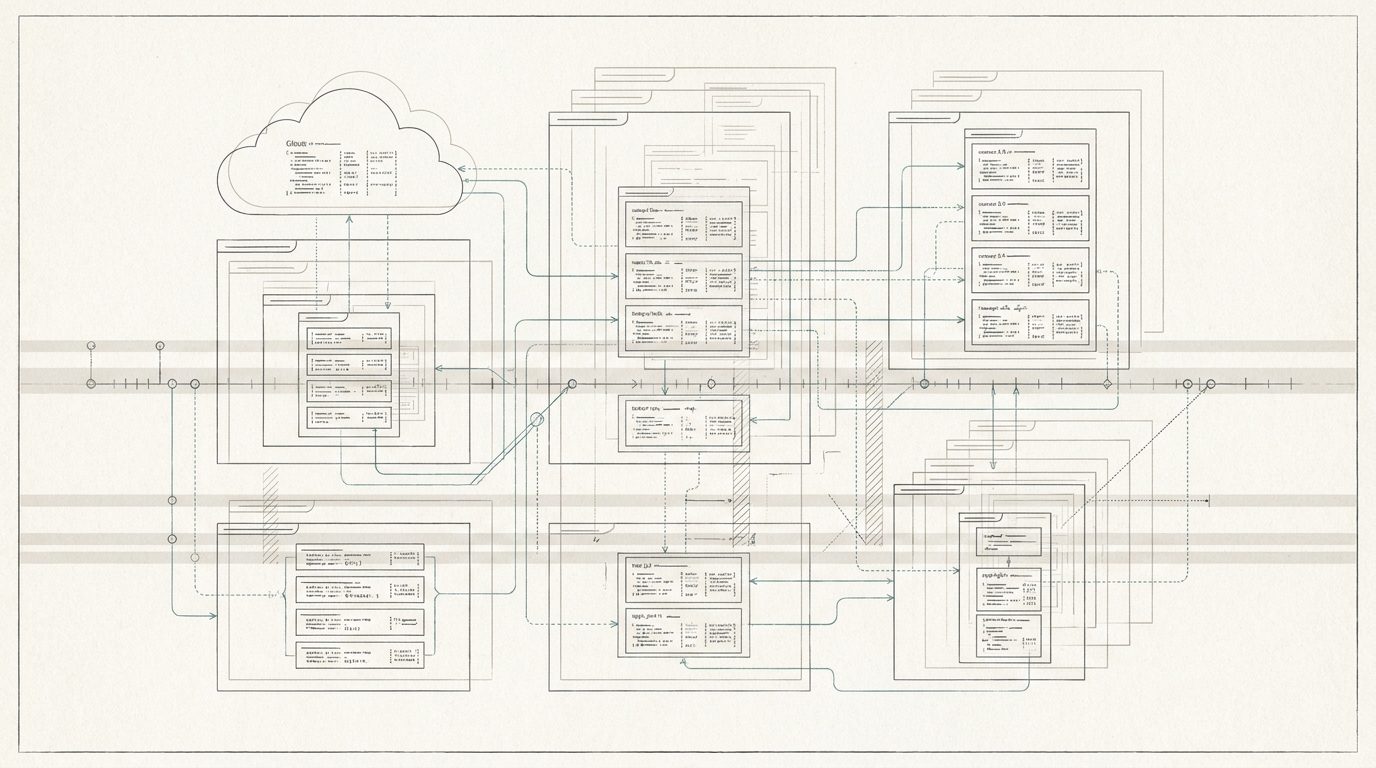
Modern organizations often require shared devices that provide controlled access to applications, internal systems, or public services. These environments must remain secure, compliant, and easy to manage without introducing operational complexity.
Example capabilities include:
- Entra ID–joined shared devices with controlled authentication
- Conditional Access–based restrictions for applications and resources
- Secure browser or application lockdown for kiosk scenarios
- Automated provisioning and reprovisioning workflows
- Session control and user isolation on shared machines
These architectures ensure that shared devices remain secure, maintainable, and aligned with enterprise governance requirements while still providing a seamless user experience.