Cross-Service Root Cause Intelligence
Clear, evidence-backed explanations grounded in tenant data.
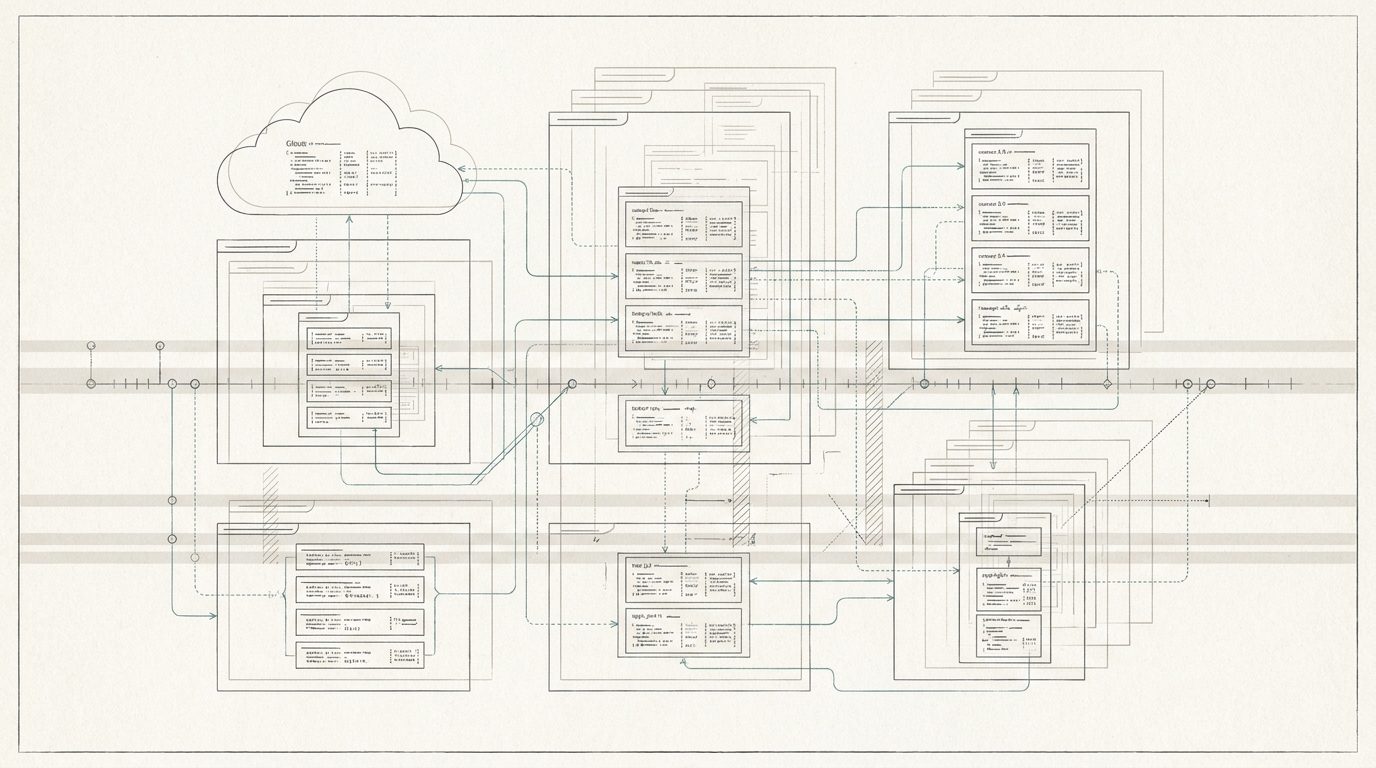
Cross-Service Root Cause Intelligence is Panorama AI’s ability to connect signals across identity, devices, applications, and policies to explain why something happened, not just what happened. Instead of analyzing events in isolation, Panorama AI correlates data across systems like Entra ID, Intune, Microsoft 365, Azure, and endpoints, building a unified chain of events. By linking changes to downstream impact and identifying affected users, devices, and services, it delivers clear, evidence-backed explanations grounded in real-time tenant data.
Eliminate root cause ambiguity across your Microsoft environment.
Modern Microsoft environments are deeply interconnected, but operational data remains siloed. A single issue, like MFA failures or compliance drops, can originate from changes in entirely different services. Teams are left chasing symptoms across multiple tools, manually reconstructing timelines, and repeatedly asking, “What changed?” This fragmentation leads to slow investigations, misidentified root causes, and recurring incidents. The challenge isn’t a lack of data, it’s the inability to connect the date into coherent, actionable intelligence.
From guesswork to definitive root cause.
Panorama AI transforms scattered, cross-service data into precise, explainable insights. Instead of guesswork and escalation, teams receive clear narratives that link cause and effect, reducing Mean Time To Resolution (MTTR), improving root cause accuracy, and preventing repeat incidents. By automatically correlating changes across services and surfacing their real impact, it enables faster, more confident decision-making at every level of IT. The result: root cause identification in a fraction of the time, fewer escalations, more durable fixes, and a system that finally makes sense end-to-end.