
IDENTITY
Access decisions drift faster than policy
Conditional Access, role assignments, and trust assumptions become inconsistent when identity architecture is not actively governed through operations.
Microsoft Cybersecurity
Veles IT Solutions provides Microsoft cybersecurity services that align identity, endpoint trust, governance, and security operations into a control model teams can enforce, manage, and sustain.
Across the market, cybersecurity is increasingly framed around resilience, response, and digital-core protection. In practice, the failure mode is that identity, device trust, governance, and operations still run as separate conversations, so the controls never become as coherent as they need to be.

IDENTITY
Conditional Access, role assignments, and trust assumptions become inconsistent when identity architecture is not actively governed through operations.

DEVICES
Endpoint posture, patch state, compliance, and control logic lose force when they are disconnected from the identity and security model.

OPERATIONS
Monitoring and response readiness only matter when they result in clearer ownership, better escalation, and more reliable control changes.

GOVERNANCE
Audit and regulatory expectations create pressure, but the actual control layers remain too fragmented to stay enforceable over time.
That is why Veles treats cybersecurity as a Microsoft operating model problem as much as a control problem.
Entra ID, Conditional Access, role design, and access decisions structured around real operating requirements and risk boundaries.
Device compliance, security posture, Defender alignment, and trust relationships that support stronger access and control decisions.
Baselines, reporting, auditability, and exception handling that make security decisions easier to justify and sustain.
The strongest cybersecurity offerings in the market combine strategy, protection, resilience, and operations. In Microsoft environments, that translates into identity-led security, endpoint trust, governance, and response readiness built to work together.
Monitoring, escalation, and response-readiness decisions that connect operational teams to the actual control model.
Practical role boundaries, access discipline, and privilege decisions that reduce ambiguity without making the platform harder to run.
A security posture that can hold up under disruption because it has been designed for operations, recovery, and change.
That is what turns security from a policy exercise into a durable operating model.
Conditional Access, role boundaries, Defender posture, and endpoint compliance all depend on the same trust story. If those layers drift apart, security decisions become harder to enforce.
Veles connects the control model across identity, device, application, and governance decisions so security is more than a list of enabled features.
Security architecture only holds up when exceptions, alerts, role changes, endpoint state, and audit evidence have a clear operating cadence.

Identity-led control models for Entra, Conditional Access, device trust, and passwordless security posture.
Learn moreReporting, baselines, auditability, and exception logic that strengthen cybersecurity enforcement.
Learn moreEndpoint and policy design choices that shape device trust, compliance, and the day-two security model.
Learn moreEndpoint control and policy execution that support stronger security posture across Windows environments.
Learn moreApplication control, privilege governance, and lifecycle discipline that influence the security model more than many teams expect.
Learn moreOperational reporting and response-oriented automation that can reduce manual drag in security operations.
Learn moreSecurity programs tend to work better when these areas are designed together instead of treated as unrelated projects.
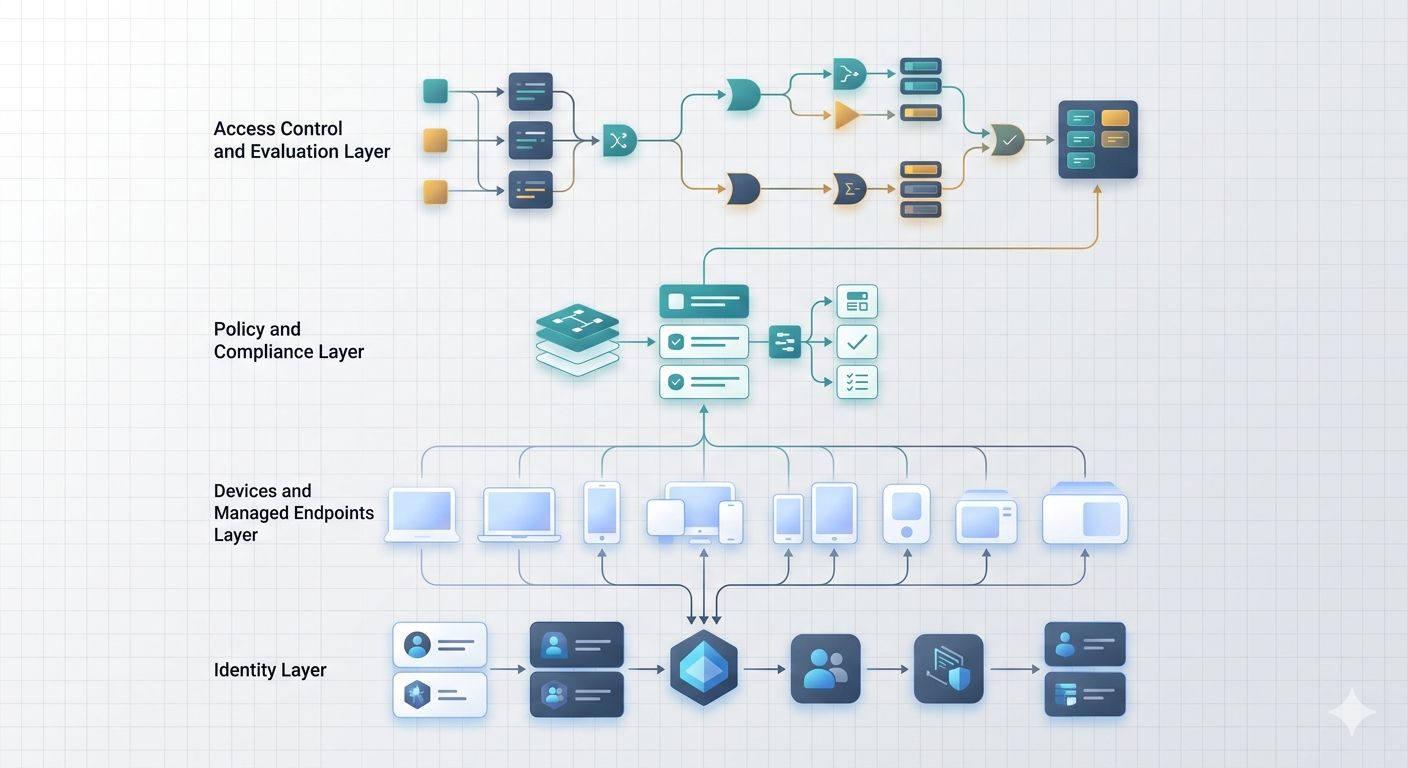
A single visual anchor keeps the section focused on the way identity, endpoint trust, governance, and resilience have to reinforce each other after design work is complete.
Role design, Conditional Access, and device compliance are reviewed as one decision model instead of separate security and endpoint tracks.
Reporting, baselines, and exception handling are shaped so teams can explain how controls are enforced and why changes were made.
Response, recovery, and operational ownership are considered alongside control design so security can survive disruption and change.
Identity, endpoint trust, governance, and response readiness designed as one Microsoft security operating model.
The work has to move from risk visibility to enforceable controls and then into operations that can keep those controls healthy under change.
Review how identity, devices, compliance, operations, and governance currently interact and where the control model is weakest.
Define the access, device, governance, and resilience decisions that need to be enforced consistently across the environment.
Translate the design into Microsoft-native controls, reporting logic, and operational processes that teams can actually sustain.
Make the environment easier to monitor, review, and evolve without letting security posture degrade between major projects.
That is what turns security from a policy exercise into a durable operating model.
Cybersecurity FAQ
Veles focuses on Microsoft-centric cybersecurity across identity, endpoint trust, access control, governance, compliance, resilience, and security architecture that teams can actually operate.
No. Veles is not positioned as a generic security monitoring provider. The emphasis is on architecture-led cybersecurity that aligns policy, access, device trust, compliance, and operational control inside Microsoft environments.
Yes. Engagements can span cyber risk assessment, control design, technical implementation, operational hardening, and ongoing alignment with governance or regulatory expectations.
They are part of the same design problem. Security controls, reporting, exception handling, and auditability should be integrated instead of treated as separate tracks.
Yes. In Microsoft estates, cybersecurity usually works best when endpoint architecture, Entra ID, Conditional Access, compliance, and operations are improved together rather than in isolation.
Start with a discussion of identity, endpoint, governance, and resilience decisions that need to become more coherent in your environment.