The Hidden Bottleneck Slowing Your IT Teams
Modern enterprise environments generate enormous volumes of operational data. Every configuration change, authentication event, compliance update, and system alert leaves a trail.
Yet when something breaks, teams still face a surprisingly manual challenge. Investigating an operational issue often requires administrators to search across multiple administrative portals, dashboards, audit logs, and monitoring tools. Engineers reconstruct timelines by stitching together configuration changes, authentication events, alerts, and system activity across multiple services.
What should take minutes frequently takes hours, or even days.
And while monitoring platforms have improved dramatically at detecting problems, the process of understanding what actually happened remains slow and fragmented.
For many organizations, IT incident investigation has quietly become one of the biggest operational bottlenecks in modern IT operations.
What is IT incident investigation?
IT incident investigation is the process of identifying the root cause of operational or security-related issues by analyzing logs, configuration changes, authentication activity, and system alerts across IT environments. The goal is to understand what happened, when it occurred, and which systems were affected so teams can resolve incidents faster.
Why Investigating IT Incidents Still Takes So Long
Most organizations already collect the operational data required to understand incidents.
The problem is not visibility. The problem is interpretation.
Investigating an incident often requires engineers to manually gather signals from multiple systems:
- Identity platforms
- Security monitoring tools
- Device management systems
- Application monitoring services
- Configuration management tools
- Audit logs
Each system provides part of the story. But rarely the entire explanation.
As a result, engineers often spend the majority of investigation time doing something surprisingly basic: data gathering.
The Reality of a Typical Investigation
When an alert appears, the investigation process typically follows a familiar pattern.
An engineer receives an alert indicating an authentication failure spike or a service outage. The first step is opening the monitoring tool to confirm the issue.
From there, the investigation expands.
Engineers check authentication logs to determine whether user activity has changed. They review configuration history to identify recent policy updates. They examine device compliance reports to see if endpoints suddenly failed compliance checks.
If nothing obvious appears, the search continues across additional systems. Each step adds more fragments of context. And assembling those fragments into a coherent timeline is still largely a manual process.
The Hidden Cost of Manual Investigation
This fragmented workflow has consequences beyond simple inconvenience. Slow investigation cycles introduce operational risk across the organization.
Downtime lasts longer
The longer it takes to identify the root cause of an issue, the longer systems remain degraded or unavailable.
Security exposure increases
If an authentication anomaly or configuration change triggered the issue, delayed investigation can increase exposure time.
Engineering productivity suffers
Highly skilled engineers often spend hours gathering information before they can begin solving the problem.
Decision-making slows
Without clear operational context, teams hesitate to take corrective action.
Over time, these investigation delays compound across the organization.
What Faster Incident Investigation Should Look Like
To improve investigation speed, organizations must rethink how operational signals are analyzed. Instead of treating operational data as isolated logs and dashboards, teams need the ability to understand events as connected sequences of activity.
Imagine an investigation process where engineers could simply ask:
- What changed in Conditional Access yesterday?
- Why are users failing MFA today?
- When did device compliance levels drop?
- What configuration change affected this application?
Rather than manually searching across systems, the platform would analyze operational signals across services and reconstruct the timeline automatically.
The result would be a clear explanation:
- Which change triggered the issue
- What happened
- When it happened
- Which systems were affected
This is the shift from manual troubleshooting to operational intelligence.
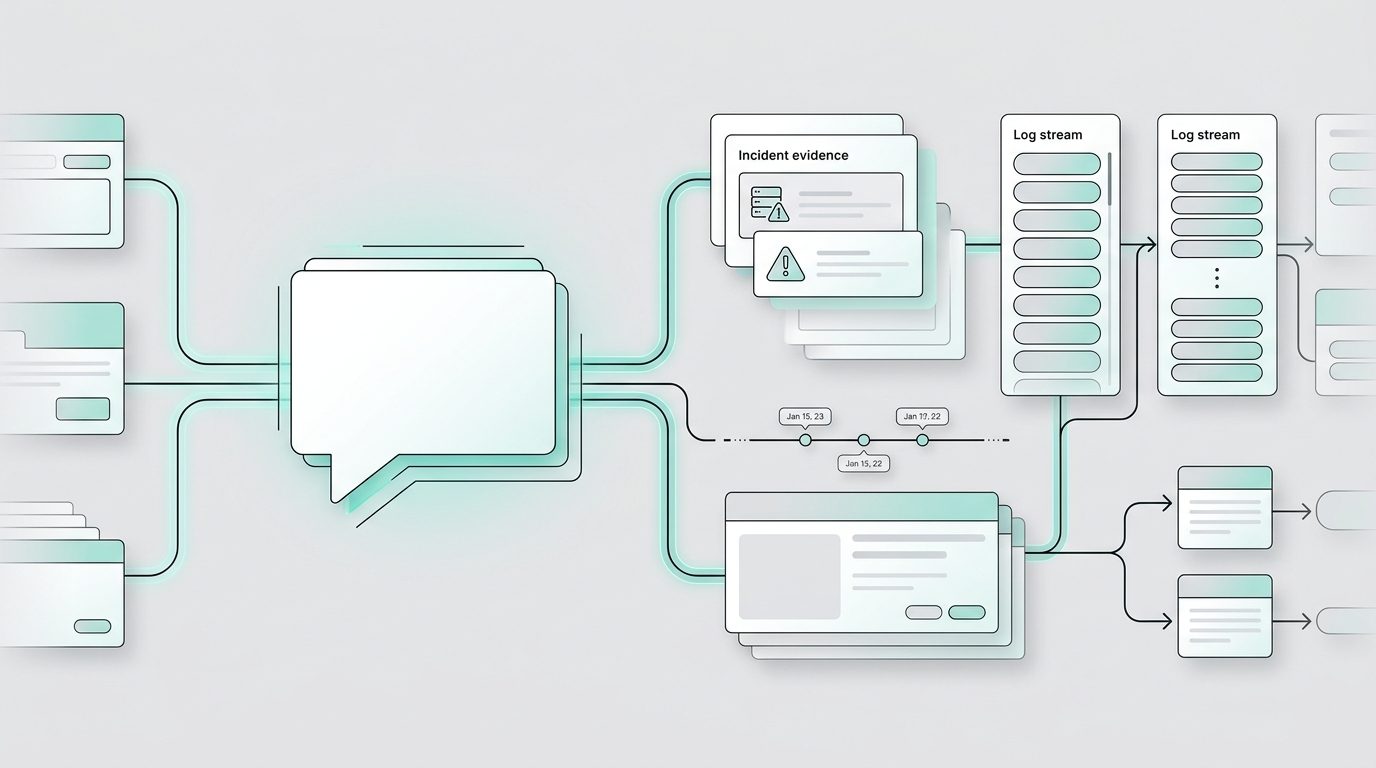
Introducing Panorama AI: A Smarter Approach to IT Incident Investigation
To address this challenge, we built Panorama AI, a platform designed to transform how organizations investigate IT incidents.
Panorama AI enables administrators to investigate incidents using natural language questions instead of manual log searches.
Behind the scenes, the platform analyzes operational signals across services, including:
- Configuration changes
- Authentication activity
- Audit logs
- Device compliance data
- Policy updates
- System alerts
By correlating these signals automatically, Panorama AI reconstructs the sequence of events that led to an issue. Instead of piecing together fragmented data, administrators receive an evidence-based explanation of the incident. This allows teams to move directly from data collection to resolution.
How Panorama AI Accelerates IT Incident Investigation
Panorama AI was designed around a simple principle: Engineers shouldn’t have to search for answers. They should be able to ask questions.
Following are several ways the platform accelerates investigation workflows.
Natural Language Investigation
Traditional investigation tools require engineers to understand log structures, filtering queries, and multiple system interfaces. Panorama AI removes this barrier.
Administrators can simply ask questions like:
- Why are users failing MFA today?
- What changed in Conditional Access yesterday?
- When did device compliance levels drop?
- Which configuration change impacted this application?
The platform analyzes relevant operational signals and produces a contextual explanation. This dramatically shortens the time required to perform investigate IT incidents.
Cross-System Signal Correlation
Many operational tools operate in isolation. Identity logs exist in one platform. Device compliance data appears in another. Configuration changes are tracked somewhere else. Panorama AI correlates these signals automatically.
For example, an investigation might reveal:
- A Conditional Access policy change occurred at 09:12 AM
- MFA failures began increasing at 09:15 AM
- Device compliance failures rose shortly after
By connecting these signals, Panorama AI reconstructs the true sequence of events.
Automated Timeline Reconstruction
One of the most time-consuming aspects of investigation is manually reconstructing a timeline. Engineers must compare timestamps across systems to determine which event triggered the issue. Panorama AI automates this process.
The platform reconstructs the timeline of events leading to an incident, showing:
- Configuration changes
- Authentication events
- System alerts
- Policy updates
- Device compliance changes
Instead of manually assembling the narrative, teams receive a structured explanation of the incident.
A Real-World Example: Investigating an MFA Failure Spike
Consider a common scenario.
An organization suddenly experiences a surge in multi-factor authentication failures. Users report login issues, and monitoring tools generate alerts.
Without operational intelligence, the investigation may involve:
- Reviewing authentication logs
- Checking recent policy changes
- Examining device compliance reports
- Searching for configuration updates
- Comparing timestamps across systems
This process can take hours. With Panorama AI, the investigation looks very different. An administrator simply asks: “Why are users failing MFA today?” Panorama AI analyzes relevant cross-service signals and produces a timeline.
The platform identifies that:
- A Conditional Access policy change occurred earlier that morning
- The policy introduced stricter device compliance requirements
- Devices failing compliance began triggering MFA failures
Within minutes, the team understands the root cause.
The Business Impact of Faster IT Incident Investigation
Accelerating investigation workflows delivers benefits beyond technical efficiency. Organizations that improve their IT incident investigation capabilities experience measurable operational gains.
Faster incident investigations
Teams can identify root causes in minutes rather than hours.
Reduced Mean Time to Resolution (MTTR)
When teams understand incidents faster, they resolve them faster.
Improved security response
Faster investigation helps identify suspicious activity and configuration changes earlier.
Increased operational visibility
Leadership gains clearer insight into how operational issues occur.
More confident decision-making
Evidence-backed explanations reduce uncertainty during incident response.
Together, these improvements transform incident response from a reactive process into a strategic operational capability.
From Troubleshooting to Operational Intelligence
Traditional investigation workflows treat operational data as something engineers must manually interpret.
Operational intelligence platforms take a different approach. Instead of expecting engineers to analyze raw data, the platform analyzes operational signals and delivers explanations.
Panorama AI represents this shift. By combining cross-system signal correlation with natural language investigation, the platform enables teams to move from manual troubleshooting toward rapid, evidence-driven IT incident investigation.
The goal is simple: reduce the time between detection and understanding.
Accelerate Incident Investigation with Panorama AI
As organizations continue to modernize their infrastructure, faster IT incident investigation will become a core operational capability. Operational intelligence platforms like Panorama AI are helping teams meet that challenge.
The longer it takes to understand an incident, the longer systems remain disrupted. Panorama AI helps organizations shorten this gap by transforming fragmented operational signals into clear explanations of what happened and why. Instead of spending hours searching logs and dashboards, teams can focus on resolving the issue.
If your organization is looking to improve IT incident investigation, Panorama AI provides a faster, smarter way to understand operational events.
Operate Your Microsoft Environment with Clarity
Panorama AI is an operational intelligence layer purpose-built for IT teams managing complex Microsoft ecosystems and spending too much time addressing change-related incidents.
Panorama AI eliminates the visibility gap across Microsoft services and endpoints to provide a unified system view, including granular configuration intelligence, complete change transparency, and persistent operational memory of every incident and resolution.
By combining natural language investigation with advanced AI, Panorama AI empowers IT teams to reduce investigation times, escalations, and MTTR (Mean Time to Resolution). Through tenant-specific cross-service root cause intelligence and proactive configuration drift monitoring, Panorama AI reduces incident frequency (both new and repeat incidents).
No more chasing alerts. No more jumping between tools. No more manually reconstructing timelines.
Instant understanding of what changed, what it impacted, and how to fix it.
Schedule a demo or connect with one of our experts today to see how you can bring clarity, speed, and control to your operations.